The Essential Role of Okta Backup in Cyber Security
Identity and access management (IAM) systems like Okta are the gatekeepers of organizational security. However, even these ‘secure’ systems, are not immune to cyber risks. As cyber threats evolve, relying solely on Okta’s native security features without a comprehensive backup strategy can leave your team vulnerable to attacks.
Okta provides a secure platform that provides many resiliency features, but the onus of data protection ultimately falls on you, the customer. This article details the importance of backing up Okta data to reduce cyber risks, specific backup strategies and the potential costs of IAM data loss.
The Importance of Keeping Identities Secure
Cyber Risk Statistics
Okta is scaling to 50 Billion users globally, meaning that there is a tremendous increase in potential for hackers trying to expose users and identities.
According to a report by Cybersecurity Ventures, cybercrime is expected to cost the world $10.5 trillion annually by 2025. A significant portion of these attacks target identity systems, aiming to gain unauthorized access to sensitive data and systems.
"There are 30 million small businesses in the U.S. alone that need to stay safe from phishing attacks, malware spying, ransomware, identity theft, major breaches and hackers," says Scott Schober, author books “Hacked Again” and “Cybersecurity Is Everybody’s Business.”
81% of hacking-related breaches leveraged stolen or weak passwords (Verizon 2020 Data Breach Investigations Report).
The Cost of Not Backing Up Data
Financial Impact
The average cost of a data breach in 2023 was $4.45 million, according to IBM’s Cost of a Data Breach Report. Organizations will continue to face increased recovery costs, legal fees, and potential regulatory fines.
Potential revenue loss due to system downtime is steadily increasing and is currently up to $540,000 per hour for large enterprises (Gartner).
Regulatory fines: Up to 4% of global annual turnover under GDPR.
Reputational Damage
Data breaches and identity compromises can severely damage an organization’s reputation, leading to lost business opportunities and diminished customer trust.
Operational Disruption
Identity systems are critical for day-to-day operations. A cyber attack on Okta could lock out all employees, bringing operations to a standstill. Any disruption can lead to significant productivity losses in days-to-weeks-to-months and impact your organization’s ability to serve your customers.
What Does Okta Back Up
- Infrastructure Security: Ensures the availability and integrity of Okta’s services.
- Basic Redundancy: Provides basic failover and redundancy to prevent service disruptions.
What Organizations Need to Back Up
- Identity Data: User profiles, group memberships, and authentication policies.
- Configuration Data: Application integrations, security policies, and custom configurations.
- Audit Logs: Detailed logs of user activities, changes, and access patterns.
How Okta Backup Enhances Security
Data Protection
Regular backups of identity and configuration data ensure that organizations can quickly restore their Okta environment to a known good state in the event of a cyber attack or accidental data loss.
Compliance
Many regulatory frameworks, such as GDPR and HIPAA, mandate the protection and availability of identity data. Regular Okta backups easily help organizations meet these compliance requirements and avoid hefty fines.
Business Continuity
In the event of a cyber attack, having a reliable Okta backup ensures minimal disruption to business operations. Organizations can quickly restore access controls and continue functioning without significant downtime.
What Okta Data Needs Backup?
The critical Okta data elements requiring backup include:
- User profiles and attributes
- Group memberships
- Application assignments
- Authentication policies
- Multi-factor authentication (MFA) settings
- API tokens and integrations
- Custom scripts and workflows
An effective Okta backup strategy should also include:
- Regular, automated Okta backups
- Versioning to track changes over time
- Encrypted storage of backup data, as well as WORM enabled on the storage to prevent encryption and/or deletion attempts of backed up data
- Geographically dispersed backup locations
- Periodic scheduled restore testing to ensure data integrity and functionality
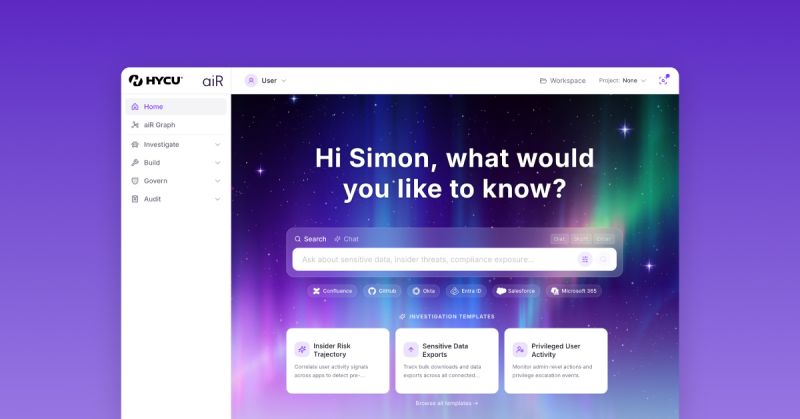
Maximize the benefits of Okta backup with HYCU
- Conduct a thorough data audit to identify all critical Okta elements
- Establish clear retention policies aligned with compliance requirements
- Implement least-privilege access for backup management
- Regularly test restore procedures to ensure recoverability
- Integrate Okta backup strategy into your broader disaster recovery strategy
Conclusion
In an era where digital identities are prime targets for cybercriminals, Okta backup strategy is not just a best practice—it's a necessity. Don't wait for a catastrophic data loss to act. Secure your Okta environment today and safeguard the digital identities that are the lifeblood of your organization.
By investing in a reliable Okta backup solution like HYCU, organizations can significantly reduce cyber risks, mitigate the financial, operational, and reputational impacts of data breaches and ensure their identity data remains secure in the face of evolving cyber threats.
Ready to protect your Okta data against cyber threats? Contact HYCU for a personalized demo and see how our Okta backup solution can enhance your organization's security posture.
Related Resources:
Get the newest insights and updates
By submitting, I agree to the HYCU Subscription Agreement , Terms of Usage , and Privacy Policy .